At Google Cloud, we work tirelessly to give our customers increased levels of control and visibility over their data. Today in London at Next UK, we’re announcing new capabilities for data encryption, network security, security analytics, and user protection designed to deliver on that promise.
External Key Manager: Store and manage encryption keys outside of Google Cloud
We give enterprises a broad range of encryption options so you can appropriately balance risk, control, security, and operational complexity when protecting your cloud workloads.
Google Cloud encrypts customer data-at-rest by default and offers customers multiple options to control and manage their encryption keys. Today, we’re pleased to announce the next level of control with our new External Key Manager. Coming soon to beta, External Key Manager works with Cloud KMS and lets you encrypt data in BigQuery and Compute Engine with encryption keys stored and managed in a third-party key management system deployed outside Google’s infrastructure. External Key Manager allows you to maintain separation between your data-at-rest and your encryption keys while still leveraging the power of the cloud for compute and analytics.
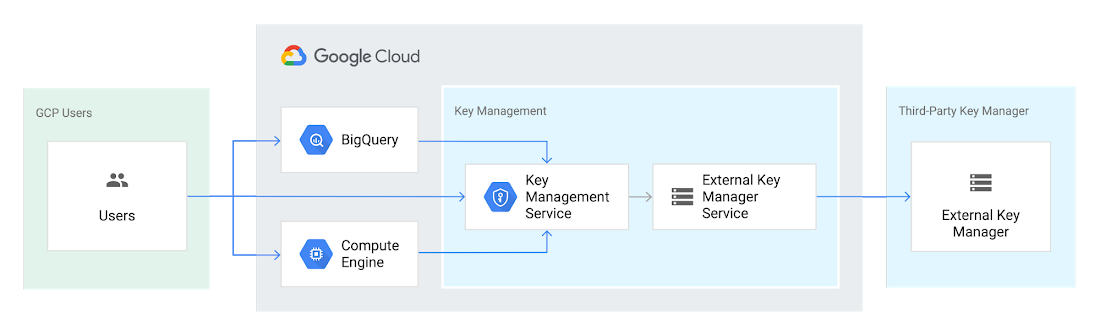
To make this new service easy to implement, we are working with five industry-leading key management vendors: Equinix, Fortanix, Ionic, Thales, and Unbound.
Key Access Justifications: Decide when and why your data can be decrypted
We believe that trust in the cloud is created through transparency. Google Cloud led the industry in providing meaningful transparency into providing access to customer data, and now we’re extending that transparency to the use of encryption keys. Key Access Justifications is a new feature that will work with the External Key Manager. It provides a detailed justification each time one of your keys is requested to decrypt data, along with a mechanism for you to explicitly approve or deny providing the key using an automated policy that you set.
Using External Key Manager and Key Access Justifications together, you can deny Google the ability to decrypt your data for any reason. As a result, you are the ultimate arbiter of access to your data–a level of control not available from any other cloud provider. Key Access Justifications is coming soon to alpha for BigQuery, and Compute Engine/Persistent Disk and covers the transition from data-at-rest to data-in-use. Customers interested in becoming early adopters can sign up here.
These new encryption innovations complement other recently released encryption options:
- Customer-managed encryption keys for Cloud SQL, now generally available (GA)
- Customer managed encryption keys for GKE persistent disks, a beta feature for Google Kubernetes Engine (GKE)
- Application layer secrets encryption in GKE, a GA feature which enables envelope encryption for your Kubernetes secrets
- Key import for Cloud HSM, a GA feature which lets users generate and use their own keys with Google Cloud’s managed HSM service
- Cloud HSM availability in all Google Cloud regions and multi-region (with the exception of global multi-region)
All these updates offer you more control over how your data is protected.
Defend against internet threats
When you stand up applications on Google Cloud, you benefit from DDoS and web attack protection at Google scale. Google Cloud Armor works with our global Cloud Load Balancing infrastructure and provides always-on attack detection and mitigation so you can run your business without interruption.
Today, we’re pleased to announce the beta of Cloud Armor’s new web application firewall (WAF) capabilities to help protect applications against targeted and distributed internet threats. You can now configure Cloud Armor policies with geo-based access controls, pre-configured WAF application protection rules to mitigate OWASP Top 10 risks, and a custom rules language to create custom Layer-7 filtering policies.
Cloud Armor also now integrates with Cloud Security Command Center (Cloud SCC), notifying customers of suspicious application traffic patterns directly in the Cloud SCC dashboard.
Collect and inspect network traffic at scale
As networks grow in complexity, monitoring traffic helps you manage performance and security. In public cloud environments, however, capturing network traffic reliably at scale for monitoring has been a challenge.
Our new Packet Mirroring service, now in beta, allows you to collect and inspect network traffic for Compute Engine and GKE; it’s available for all machine types in all of our regions. With this service, you can use third-party tools to more proactively detect threats, better respond to intrusions with signature-based attack detection, and better identify zero-day attacks with anomaly detection. For more, watch this video.

We’ve built an ecosystem of partners so you can use Packet Mirroring with third-party tools of your choice, including products from Awake Security, Check Point, Cisco, Corelight, cPacket Networks, ExtraHop Networks, Flowmon, Ixia by Keysight, Netscout, and Palo Alto Networks.
Protect G Suite and Cloud Identity users
Google’s Advanced Protection Program is our strongest protection for users at risk of targeted attacks. In the enterprise, this includes IT administrators and executives. Today, the Advanced Protection Program is starting to roll out to G Suite and Cloud Identity customers. With the Advanced Protection Program for the enterprise, we’ll enforce a specific set of policies for enrolled users including security key enforcement, blocking access to untrusted apps and enhanced scanning for email threats. Learn more.

We’re also introducing app access control, helping you reduce the risk of data loss by limiting access to G Suite APIs to third-party apps you trust. You can also more easily manage and restrict which Google APIs are available for use by third-party and customer-owned apps, and see which apps are verified by Google. Learn more.
Benefit from unique Google threat intelligence in Cloud Security Command Center
We continue to build products that help our customers benefit from the techniques we’ve developed to defend Google. Whether you are using Cloud Security Command Center to improve your security posture on GCP, or Chronicle Backstory to monitor your data on-premise or in other clouds, we’re packaging threat detection and prevention capabilities that are available only from Google and giving them to you.
Event Threat Detection, now in beta, helps you detect threats targeting your cloud resources using logs, so you can send incidents to your SIEM (Security Information and Event Management system) for further investigation. Event Threat Detection relies on Google threat intelligence to help you spot and stop threats before they result in business damage or loss.
Security Health Analytics helps you prevent incidents by identifying potential misconfigurations and compliance violations in your GCP resources and suggesting appropriate corrective action.
As we continue to innovate and simplify security management on GCP, Event Threat Detection and Security Health Analytics will be bundled in a Premium Edition of Cloud Security Command Center with other new capabilities that help you meet industry compliance requirements, catch web application vulnerabilities, detect compromised VMs, and discover other threats. The Premium Edition will give you a comprehensive, easy-to-deploy set of tools to protect your cloud resources. To learn more about how to use Cloud Security Command Center, check out our recent video series.
Chronicle: security analytics wherever your apps are deployed
Chronicle’s Backstory product was designed by former Google security professionals to enable anyone to use the types of techniques we use to detect threats and investigate security incidents. It brings world-class strengths in data analytics to your security data, privately and easily.
Many organizations leverage a mix of on-prem environments and multiple clouds to run their applications, making it difficult to collect and store security telemetry from various systems and tie individual events together for analysis. Backstory, our flagship offering for hybrid security analytics, offers you this level of intelligence. With just a few clicks, in minutes, you can aggregate and analyze your security telemetry wherever your apps may run, and where they might run in the future.
Be sure to check out the Chronicle booth during Next UK to learn more!
Learn more
With these capabilities, we continue to innovate and empower Google Cloud customers with advanced security functionality that is easy to deploy and use. Learn more about our entire portfolio of security capabilities in our Trust & Security Center. Learn More